How Attackers are Taking Advantage of the Exchange Server Vulnerabilities?
Summary: Recent ransomware attacks on Microsoft Exchange servers, such as Hafnium, LockFile, etc., have put the Exchange Server security into the spotlight. Although Microsoft continues to monitor the attacks and releases updates to patch the Exchange Server vulnerabilities, there are tens of thousands of organizations that did not patch their Exchange servers yet. In this post, we’ve discussed how attackers are taking advantage of Exchange Server vulnerabilities. Also, we’ve mentioned ways to protect your Exchange Server from ransomware attacks.
Contents
This year, we have seen a significant spike in cyberattacks on on-premises Exchange servers. Multiple state-sponsored or financially motivated threat actors and groups are actively scanning and targeting vulnerabilities on on-premises Microsoft Exchange servers. The attackers are targeting organizations across all verticals worldwide. However, most of their targets and victims are from United States, UK, Netherlands, Russia, Germany, and Asia.
How Attackers are Exploiting Exchange Server Vulnerabilities?
In our earlier post, we have already shared the tactics, techniques, and procedures used by the Hafnium group to exploit the ProxyLogon vulnerability to compromise more than 30,000 organizations running an on-premises Exchange Server 2013, 2016, or 2019 version. However, post Hafnium, there have been multiple ransomware attacks that occurred on on-premises Exchange Server. The most recent is LockFile that exploited the PetitPotam bug in Exchange Server, which was partially patched by Microsoft in May this year.
It reminds us how easy it is for the attackers to exploit disclosed vulnerabilities and target unpatched Exchange servers. It also indicates how critical it is to install security updates and patches as soon as possible to prevent potential attacks.
Below are a few examples of how various attackers have taken advantage of disclosed Exchange Server vulnerabilities to carry out various ransomware attacks.
DoejoCrypt Ransomware
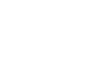
DoejoCrypt ransomware took advantage of ProxyLogon and ProxyShell vulnerabilities found in Microsoft Exchange servers. It started targeting and encrypting the unpatched Exchange servers shortly after Microsoft released the updates. The ransomware attack begins with the deployment of a Chopper web shell on the server after exploitation.
The web shell creates a batch file in the C:\Windows\Temp folder\ that performs a backup of Security Account Manager (SAM) database and System and Security registry to access the user passwords later. This gives threat actors access to the server for their future attacks if the organization fails to reset the credentials. It was also observed that the attackers could get Domain Administrator (DA) rights on systems where the batch file is present. With DA rights, the threat actors can execute the ntdutil and access all the user passwords present in the Active Directory (AD).
Pydomer Ransomware
Pydomer ransomware is build using Python and uses the Python cryptography libraries to encrypt the data on the server. It takes advantage of a combination of Exchange Server vulnerabilities to steal data from the servers. Similar to Hafnium, the attackers install web shells and a malicious PowerShell script. On successful execution, the ransomware encrypts the data on the server with the .demon extension and leaves a ransom note with the file name Readme.txt or decrypt_file.txt in one of the drives. The Pydomer web shells were observed on 1500 systems, but not all were encrypted.
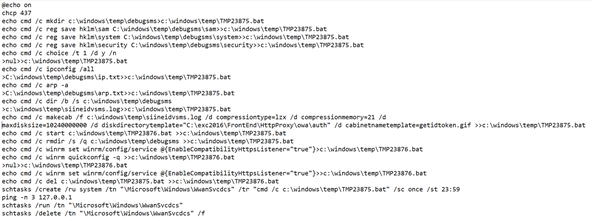
Black KingDom Ransomware
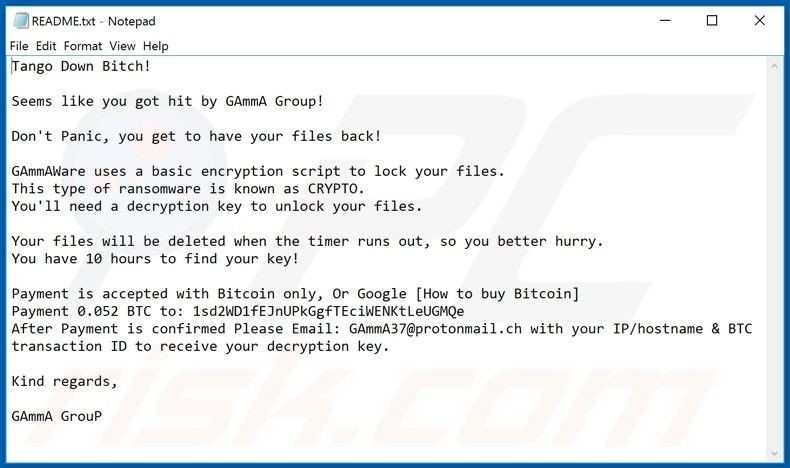
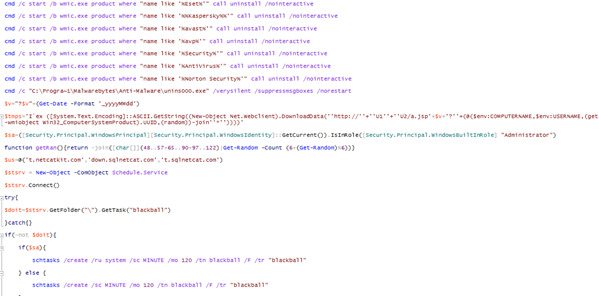
The Black KingDom is another ransomware variant that targets on-premises Exchange Servers that were not updated and were exposed to the ProxyLogon vulnerabilities. Black KingDom ransomware, also referred to as DemonWare or gAmmAWare, targets the ProxyLogon CVE-2021-26855 vulnerability to access, compromise, and deploy web shells on the unpatched Exchange servers.
Once web shells are installed, attackers use these web shells to install the ransomware, which encrypts the files with the .demon extension. It also adds a decrypt_file.txt or ReadMe.txt file similar to Pydomer ransomware.
Lemon Duck Botnet
Lemon Duck is a cryptocurrency botnet, which became a part of threat groups and attackers targeting unpatched vulnerable Exchange servers shortly after the updates were released. Instead of web shells, it used the PowerShell commands from the IIS worker process called w3wp for the attacks. They used the email-based campaigns to reach and compromise the vulnerable Exchange servers.
And instead of mining, the botnet started loading malware on the compromised servers. Access to PowerShell allowed the attackers to execute commands directly without using any web shell to download and drop a payload.
LockFile Ransomware
LockFile is a new ransomware variant that takes advantage of ProxyShell and PetitPotam vulnerabilities on the unpatched Exchange servers. Although Microsoft partially patched the PetitPotam bug, threat actors are still able to exploit it.
LockFile ransomware group uses a combination of Exchange Server vulnerabilities to target and compromise the domain controller. Once the DC is compromised, the threat actors install tools, batch files, and executables to further compromise the organization’s network and other devices on the network.

The files are copied in the sysvol\domain\scripts directory. If any client authenticates to the domain, the executable and batch files are executed, which encrypts the device data.
How to Protect Your Exchange Servers from Attacks?
Hackers and threat actors exploit the bugs and vulnerabilities in combination, such as ProxyShell, to bypass the authentication and gain access to the Exchange Server and the organization’s network. The best remedy to protect and safeguard your organization from malicious attacks is to install the latest cumulative and security updates on your server. To install Microsoft updates, refer to our detailed guide on Microsoft Exchange Remote Code Execution Vulnerability Flaws and Their Fixes.
If you suspect that your server is compromised or threats are present on your organizations’ network, use the HeathChecker.ps1 script and Exchange On-Premises Mitigation Tool (EOMT) to mitigate the risks and threats.
Conclusion
Security researchers are predicting more attacks on vulnerable and unpatched on-premises Exchange servers in the coming days as more threat actors are actively scanning for unpatched servers. The best defense is to update and patch the Exchange Server vulnerabilities. We urge you to check and install supported Cumulative Updates (CUs) and Security Updates (SUs) on your server to safeguard against malicious attacks. Strengthen your server and organization security by utilizing firewalls, application-aware antivirus tools, and educating the users. Backups are also critical. Follow the 3-2-1 backup rule to protect your data. However, if your server is compromised, use EOMT and Heath Checker script to mitigate the risks, patch your server, and preferably move the data to a new Exchange Server or Office 365. You can use an Exchange recovery software, such as Stellar Repair for Exchange, to recover mailboxes and export them to PST or restore them directly to a new live Exchange Server or Office 365.
Source: Microsoft