IcedID is a modular banking Trojan, also known as BokBot. First spotted in 2017, it is known for targeting financial information. However, it is mainly used as a dropper or loader for dropping or loading second-stage malware or ransomware on the targeted system or organization network.
Threat actors are now using the IcedID Trojan to hijack email conversations and inject the infectious payload into the target system or network through phishing attacks.
The attacks were spotted in March 2023 with possible links to November 2021 internal email reply chain attack campaign.

The attacks are being carried out using previously compromised Exchange Servers used to send malicious phishing emails, making them appear as legit emails.
How Does IcedID Attack Work?
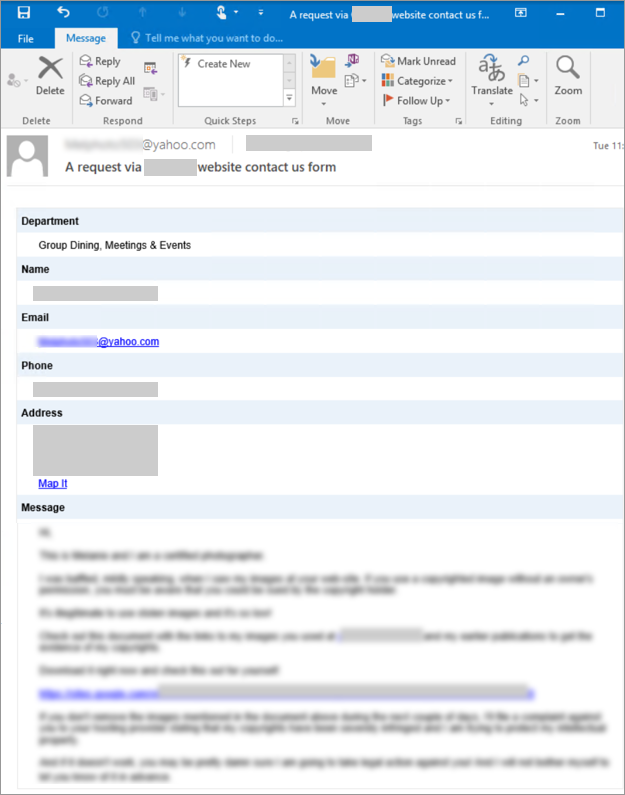
The IcedID is planted on the target systems through an email phishing campaign. The email attack uses social engineering to hijack conversations, also referred to as thread hijacking used for reply chain attacks. The email is sent with a malicious attachment to convince the user on the target system to open the attachment. The message appears as a continued conversation thread that increases the credibility and chances of opening the infectious attachment.
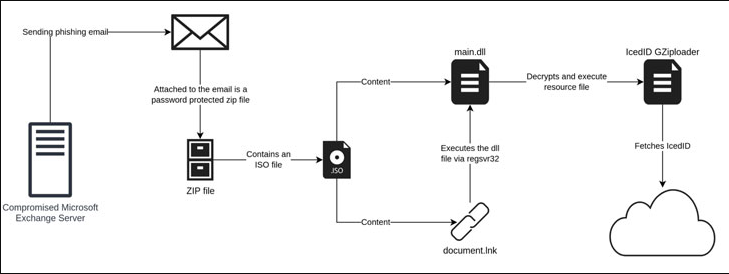 Image Source – bleepingcomputer
Image Source – bleepingcomputerThe attackers use stolen user credentials from compromised and vulnerable Exchange Servers to run the malicious email campaign and deploy the IcedID in the targeted organization’s network and systems.
The emails are sent using local IP within a trustworthy domain, making it look credible and thus, minimizing the chances of suspecting email fraud once the attachment is opened. Attackers are also taking advantage of contact forms on the websites to deliver the IcedID malware.
The ZIP attachment sent with the email contains the ISO file, enclosing a DLL and LNK file. When the user clicks on the .lnk file (documents.lnk), the DLL file deploys the IcedID GZiploader.
The IcedID GZiploader is stored in an encrypted form within the binary’s resource section. Once decoded, it is placed in memory and executed.
An HTTP GET request is then used to transmit basic system information to Command and Control Center (yourgroceries[.]top). The Command and Control Center responds to the request by delivering the payload on the targeted or infected machine.
How to Protect Your Organization from IcedID?
Upgrade and update your vulnerable Microsoft Exchange Server immediately to patch ProxyShell and ProxyLogon vulnerabilities and other security bugs. That is the best option to safeguard your mail servers and network from threat actors, ransomware, and other malicious attacks, such as IcedID.
Read our guide on how to apply the latest Cumulative Updates and Security Updates on Exchange Server.
However, if your server is compromised, it is recommended to set up a new server and restore the mailbox database from the backup. In the absence of backup, use an Exchange server recovery software, such as Stellar Repair for Exchange, to extract mailboxes from the database files on the compromised server and export them directly to the new server.
Also, follow the best practices for your Exchange Server to safeguard and protect it from various online and offline threats.