ProxyToken is the latest ‘proxy’ (authentication bypass) vulnerability that has emerged, after ProxyLogon, ProxyShell, and ProxyOracle, this year. The threat actors are actively exploiting such vulnerabilities to compromise unpatched Exchange Servers, deploy web shells, and install file-encrypting ransomware, such as LockFile, Black KingDom, etc.
The ProxyToken vulnerability allows the attackers to modify and reconfigure the mailboxes of arbitrary users. However, Microsoft released the cumulative updates to patch the vulnerability as a part of its July 2021 Patch Tuesday Updates.
The security flaw was reported via Zero-day Initiative (ZDI) by researcher Le Xuan Tuyen at the Information Security Center of Vietnam Posts and Telecommunications Group (VNPT-ISC) in March 2021.
What Is ProxyToken Vulnerability?
The vulnerability is identified and listed as,
- CVE-2021-33766: Microsoft Exchange Information Disclosure Vulnerability with a CVSS score of 7.3 that places it into the high severity group.
The ProxyToken vulnerability allows attackers to perform remote code execution in certain conditions. It allows them to reconfigure mailboxes in such a way that all the emails sent to a particular user’s mailbox are forwarded to another account. The vulnerability affects Microsoft on-premises Exchange Server 2013, 2016, and 2019.
How Attackers are Exploiting the ‘ProxyToken’ Vulnerability?
MS Exchange installation creates several Internet Information Service (IIS) virtual directories, including the two sites, one for the OWA access (frontend) and another for the ECP access (backend). The frontend works as a proxy to the backend but requires authentication to serve pages, such as /owa/auth/logon.aspx.
The frontend role is to repackage the requests and proxy them to the endpoints on the Exchange backend. After this, it collects the response from the backend and forwards it to the client. However, Exchange also supports the ‘Delegated Authentication’ feature and that’s precisely where the issue arises.
When the user authenticates, the frontend passes authentication requests to the backend using a SecurityToken cookie to identify them. However, if the frontend finds a non-empty SecurityToken cookie, it delegates authentication to the backend. By default, the DelegatedAuthModule isn’t configured to use the special delegated Authentication feature. The result is that the requests can go through to either the frontend or backend without authentication.
From there, the threat actors can configure the mailboxes and install a forwarding rule to receive and read victims’ emails. The threat actors can also configure the mailboxes of arbitrary users.
How to Protect your Exchange Server?
If you have updated your Exchange Servers with the latest Cumulative updates, no action is required. However, tens of thousands of Exchange Servers are still unpatched and vulnerable to malicious attacks.
If your server is still not updated, follow these steps to patch ProxyToken, ProxyLogon, ProxyOracle, and ProxyShell vulnerabilities on your Exchange Server and protect your organization against malicious attacks.
Step 1: Execute Exchange Server Health Checker Script
Download the HealthChecker.ps1 (Exchange Server Health Checker) PowerShell script from GitHub and then follow these steps:
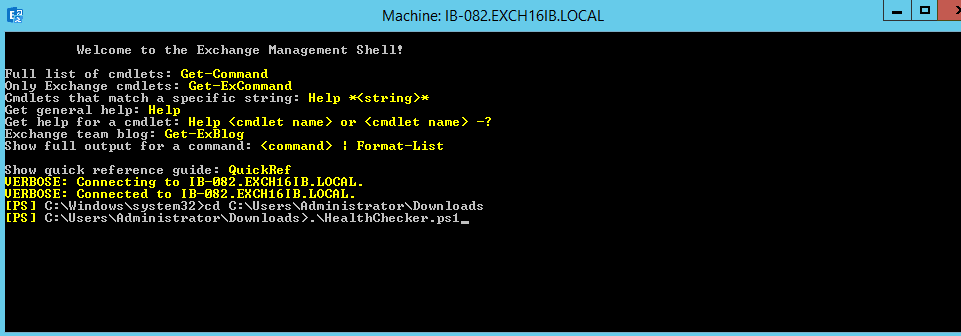
- Open EMS and navigate to the folder where HealthChecker.ps1 script is located.
- Run the following command:
.\HealthChecker.ps1
- You may also use the -server parameter to run the script for a specific server. For example,
.\HealthChecker.ps1 -Server Exch01
- In case of an error during the execution of the above commands, run the following command in EMS to bypass the execution policy (temporarily).
Set-ExecutionPolicy -Scope Process -ExecutionPolicy Bypass
The script output will display the vulnerabilities that you need to patch by installing the Microsoft Exchange cumulative and security updates.
Step 2: Run EOMT
EOMT is Microsoft’s Exchange On-Premises Mitigation tool to mitigate the risks and remove threats and web shells from the compromised server. The steps to run EOMT tool are as follows:
- Download the EOMT.ps1 PowerShell script.
- Open EMS and navigate to the location where EOMT.ps1 is located.
- Then execute the following command:
.\EOMT.ps1
- The tool runs Microsoft Safety Scanner (MSERT) in Quick Scan mode. It finds and removes threats and web shells installed by the attacker.
Step 3: Install Exchange Server Updates
Finally, download and install the Exchange Server cumulative and security updates to patch the ProxyToken, ProxyShell, ProxyOracle, and other vulnerabilities and protect your servers from threats. Refer to our blog on Microsoft Exchange Remote Code Execution Vulnerability Flaws and their Fixes to know more about the vulnerabilities and install Exchange Server security updates.
Conclusion
ProxyToken is a new RCE vulnerability found in Microsoft Exchange Server 2013, 2016, and 2019. Although Microsoft released the cumulative updates to patch ProxyToken vulnerability in July 2021, thousands of Microsoft Exchange servers are still unpatched and vulnerable to malicious attacks. Therefore, the best defense against malicious attacks is to install the updates released by Microsoft to patch the Exchange Server. Also, maintain a regular VSS backup to prevent data loss if threat actors compromise your server. You may use an Exchange Recovery software, such as Stellar Repair for Exchange, to recover mailboxes from a compromised Exchange Server database and save them to PST or export them directly to a new live Exchange Server or Office 365.