Security researchers at Red Canary have come across a new ransomware variant called BlackByte, targeted towards unpatched organizations with ProxyShell vulnerabilities.
ProxyShell is a set of three vulnerabilities— CVE-2021-34473, CVE-2021-34523, and CVE-2021-31207—patched by Microsoft back in April and May 2021. The vulnerabilities, when chained together, allow threat actors to perform unauthenticated, remote code execution on vulnerable servers.
Characteristics of BlackByte Ransomware
BlackByte ransomware started targeting corporate victims in July 2021. They are targeting organizations in the manufacturing, food, beverage, mining, construction, and healthcare sectors located mainly in countries, such as the USA, Australia, France, Italy, Chile, Turkey, and Croatia.
The ransomware group attempts to encrypt files on the targeted server by terminating critical security, database, and mail server processes.
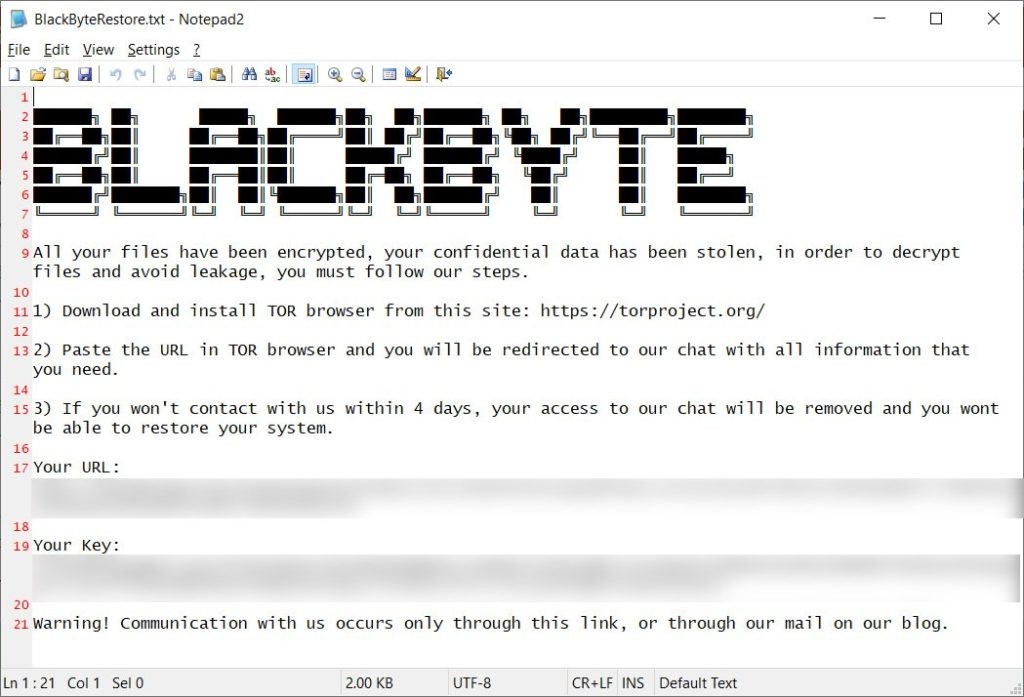 Image Source – SOCRadar
Image Source – SOCRadarFollowing are the characteristic of this newly discovered BlackByte ransomware
- BlackByte has worm functionality similar to RYUK ransomware.
- BlackByte avoids the systems with Russian or ex-USSR languages— same as other infamous ransomware, such as REvil.
- It uses only one symmetric key (AES algorithm) to encrypt the data.
How is BlackByte Ransomware Gang Compromising the Exchange Server?
After exploiting the ProxyShell vulnerabilities and gaining access to the compromised Exchange Server, the threat actors install web shells and backdoors on the server.
Web Shells are small script that allows threat actors to attain persistence and remote execute commands to perform certain actions, such as uploading additional files or malware.
The attackers use these web shells to drop a Cobalt Strike beacon— a threat simulation and penetration-testing tool—on the server.
The tool is injected into the wuauclt.exe—Windows Update Agent process and used to dump the credentials for a service account on the compromised Exchange server.
After gaining access to the service account, the adversaries install AnyDesk—a remote desktop application—to access the system and proceed to the next stage where Cobalt Strike introduces and executes the BlackByte ransomware in the compromised environment, which encrypts the data.
To avoid detection and continue the execution, the BlackByte deletes the taskmgr (Task Manager) and resmon (Resource monitor) services and stops the windefend (Windows Defender) service using an Obfuscate PowerShell command.
For more details, read this detailed report by Red Canary.
Steps to Decrypt Files Encrypted by BlackByte
Unlike other ransomware, BlackByte ransomware uses the same symmetric key to encrypt and decrypt files on compromised servers. Thus, you only need the raw key from the host to decrypt the encrypted files.
Fortunately, ‘Forest.png’—a file containing multiple AES encryption keys used by the BlackByte ransomware group to encrypt data is available.
Trustwave—leading cybersecurity and managed security service provider—wrote a free decryption tool for BlackByte ransomware, available on Github. You need to compile the code to use it for decrypting the encrypted files.
The repository also contains the Forest.png file downloaded from the hardcoded webserver—http[:]//45.9.148.114/forest.png—required to decrypt files encrypted by BlackByte ransomware. The key is likely to be reused across many victims. However, attackers may have changed it at some point.
But even if the key provided with the decryption tool does not work, you can still try it as it won’t harm your files any further.
After finding out the free decryption tool for BlackByte ransomware, the threat group claimed that some systems might fail irreversibly if decrypted incorrectly.
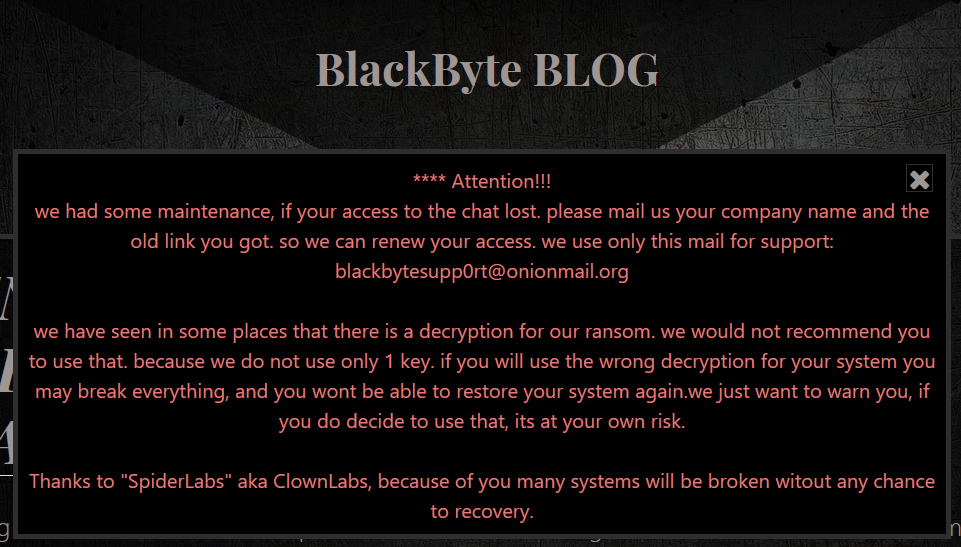 Image Source – SOCRadar
Image Source – SOCRadarSteps to Protect your Organization from BlackByte Ransomware
According to Shodan, 17,000+ Exchange Servers are still unpatched and exposed to the internet with ProxyShell vulnerabilities.
To protect Exchange Server against BlackByte and other ransomware attacks, you must immediately patch your server by following these steps.
Step 1: Check Exchange Server Health
Microsoft provides Exchange Server Health Checker Script (HealthChecker.ps1)—a PowerShell script to check the server’s health.
To get started, download the HealthChecker.ps1 available on GitHub and execute it on your Exchange Server. The script currently supports Exchange Server 2013, 2016, or 2019.
The steps are as follows,
- Open Exchange Management Shell (EMS), PowerShell, or Command Prompt as administrator and navigate to the folder location where HealthChecker.ps1 script is downloaded using the ‘cd‘ command. For instance,
cd C:\Users\UserName\Downloads\
- Then execute the following command to run the script on the server.
.\HealthChecker.ps1
- You may also generate a detailed HTML report by executing the following command.
.\HealthChecker.ps1 -BuildHtmlServersReport
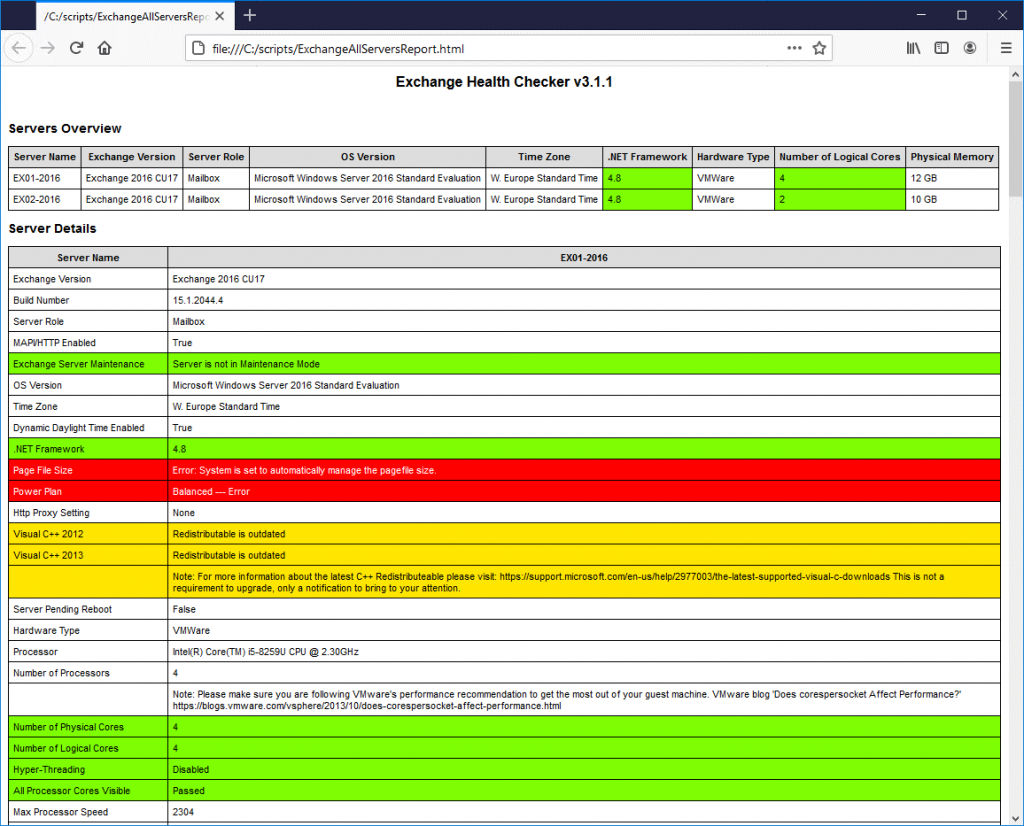
IMPORTANT NOTE: You may get a warning or error message while executing the script on your server that may prevent the script from execution. To overcome this and execute the script without any error or warning, execute the following command in EMS and execute the HealthChecker.ps1 script.
Set-ExecutionPolicy -Scope Process -ExecutionPolicy Bypass
Step 2: Download and Install Exchange Server Updates
If the report shows vulnerabilities, use the links to download the updates and install them. Refer to our detailed guide to download and install Cumulative and Security updates on Exchange Server.
Conclusion
Ransomware gangs often target unpatched Exchange Servers to exploit the vulnerabilities. The BlackByte ransomware group is found exploiting the ProxyShell vulnerability that Microsoft patched earlier this year. Thus, the best defense is to install the latest Cumulative and Security updates released by Microsoft as soon as possible.
However, in an unfortunate incident, if your server is compromised or crashed due to BlackByte, use the decryption tool discussed in this blog to recover the encrypted data.
Also, set up a new server, restore recovered data on the new server, and use the backup to restore mailboxes. You can also take the help of Exchange recovery software, such as Stellar Repair for Exchange, to recover mailboxes if the databases on the compromised server are inaccessible. The tool comes in handy when backups aren’t available, obsolete, or fail to restore the database.
To stay updated on newer threats, vulnerabilities and updates, follow our blog on Microsoft Exchange Remote Code Execution Vulnerability Flaws and Their Fixes